UltraNote specifications
Name: UltraNote.
Ticker: XUNI.
Block time target: 120 seconds.
Block reward: 5 XUNI dynamic, moving up to maximum 10 XUNI coins after 1 year.
Max Supply: 21,000,000 M coins (8 decimals)
Annual interest rate: 0.25% to 3.00% (depending on deposit term)
Algo: CryptoNight-Conceal, Proof of Work.
Mining type: CPU efficient, ASIC resistant.
UltraNote features
A decentralised privacy-protected blockchain platform.
Instant, untraceable, encrypted messages based on cryptography, involving use of One-Time Keys.
Secure CPU efficient, ASIC resistant mining.
Anonymous, instant transactions based on Ring Signatures and Double-Spending Proof.
Fair CPU-efficient ASIC-resistant Proof of Work (PoW) mining process with a dynamic base block reward = 5 XUNI moving up to maximum 10 XUNI coins.
Advanced QML GUI wallet. Full network node inside.
Multi-signatures technology in UltraNote core.
Blockchain deposits with interest based on multi-signatures technology.
Minimum transaction fee of 0.001 XUNI makes micro-payments possible.
UltraNote future development
Updated version for GUI wallet with more features.
Update CLI wallet and adding more features.
XUNI stand alone mining APP.
Building UltraNote Wiki.
Building UltraNote Web wallet.
Building mobile wallet App with integrated messenger and file sharing.
UltraNote binaries overview
UltraNote Daemon:
Default name is “ultranoteid”. Daemon is responsible for any communication with the network.
- Mining.
- Interaction with the blockchain, e.g. blocks relaying, getting info about the block, etc.
- Peer list look up.
- Connections look up.
- Transaction pool information and relaying.
UltraNoteWallet:
Default name is “ultranoteiwalletd”. It carries out basic wallet's functions:
- Wallet creation.
- Financial operations, e.g. sending, receiving, checking for incoming transfers, etc..
- ultranotewalletd also allows user to start/stop mining without a need to specify the wallet in the daemon.
- Wallet and daemon binaries work through JSON RPC.
UltraNote distributes two wallet solutions: ultranotewallet and walletd. Both daemons are capable of recieving and sending mass payouts. The difference is that walletd provides multiple wallet addresses when ultranotewallet provides only one wallet address.
UltraNote security and anonimity
Ring signatures: Untraceable payments
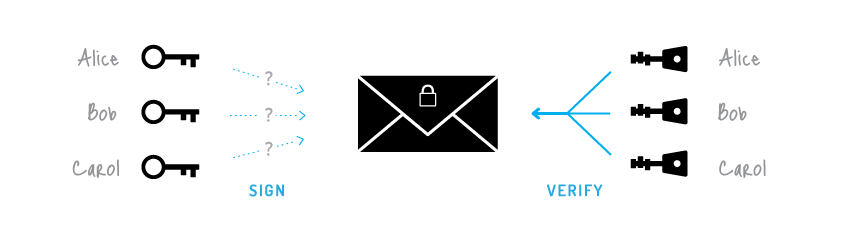
The ordinary digital signature (e.g. (EC)DSA, Schnorr, etc...) verification process involves the public key of the signer. It is a necessary condition, because the signature actually proves that the author possesses the corresponding secret key. But it is not always a sufficient condition.
 Ordinary signature
Ordinary signature
Ring signature is a more sophisticated scheme, which in fact may demand several different public keys for verification. In the case of ring signature, we have a group of individuals, each with their own secret and public key. The statement proved by ring signatures is that the signer of a given message is a member of the group. The main distinction with the ordinary digital signature schemes is that the signer needs a single secret key, but a verifier cannot establish the exact identity of the signer. Therefore, if you encounter a ring signature with the public keys of Alice, Bob and Carol, you can only claim that one of these individuals was the signer but you will not be able to pinpoint him or her.
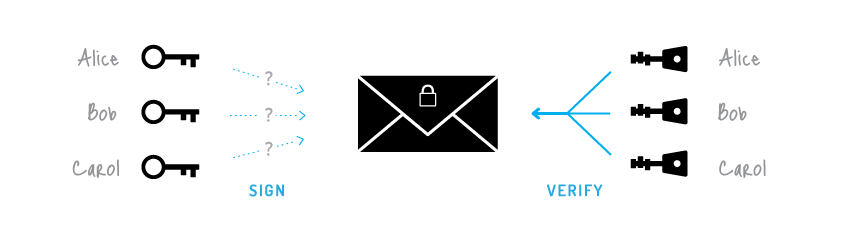 Ring signature
Ring signature
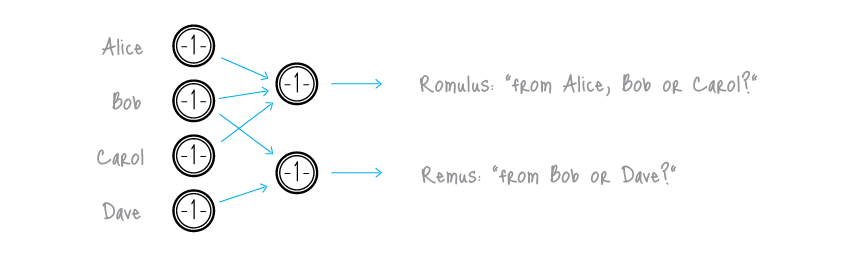
This concept can be used to make digital transactions sent to the network untraceable by using the public keys of other members in the ring signature one will apply to the transaction. This approach proves that the creator of the transaction is eligible to spend the amount specified in the transaction but his identity will be indistinguishable from the users whose public keys he used in his ring signatures.
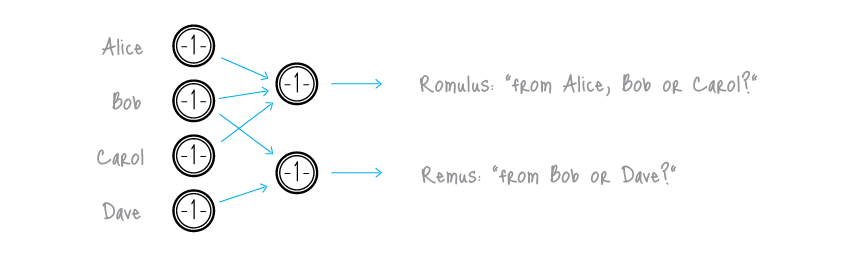 Untraceable transactions
Untraceable transactions
It should be noted that foreign transactions do not restrict you from spending your own money. Your public key may appear in dozens of others' ring signatures but only as a muddling factor (even if you already used the corresponding secret key for signing your own transaction). Moreover, if two users create ring signatures with the same set of public keys, the signatures will be different (unless they use the same private key).
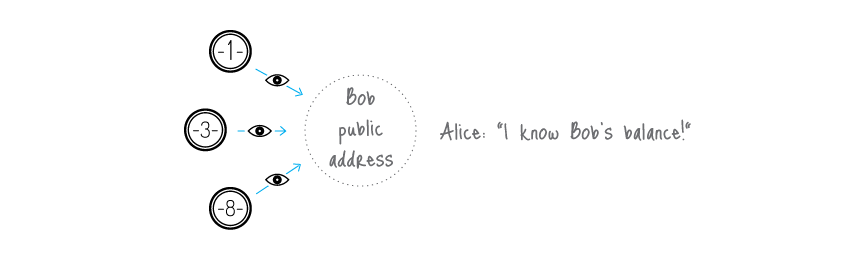
One-time keys: Unlinkable transactions
Normally, when you post your public address, anyone can check all your incoming transactions even if they are hidden behind a ring signature. To avoid linking you can create hundreds of keys and send them to your payers privately, but that deprives you of the convenience of having a single public address.
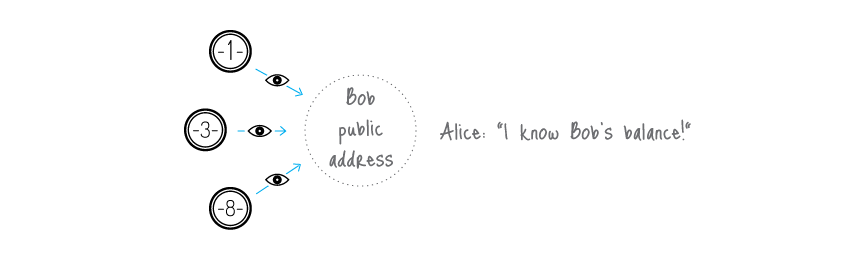 Linkable transactions
Linkable transactions
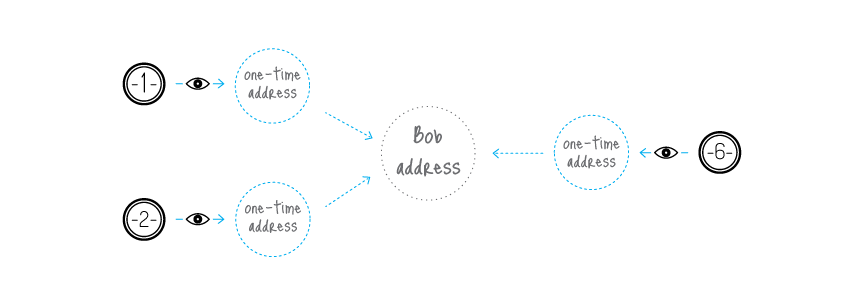
UltraNote solves this dilemma by an automatic creation of multiple unique one-time keys, derived from the single public key, for each p2p payment. The solution lies in a clever modification of the Diffie-Hellman exchange protocol. Originally it allows two parties to produce a common secret key derived from their public keys. In our version the sender uses the receiver's public address and his own random data to compute a one-time key for the payment.
The sender can produce only the public part of the key, whereas only the receiver can compute the private part; hence the receiver is the only one who can release the funds after the transaction is committed. He only needs to perform a single-formula check on each transactions to establish if it belongs to him. This process involves his private key, therefore no third party can perform this check and discover the link between the one-time key generated by the sender and the receiver's unique public address.
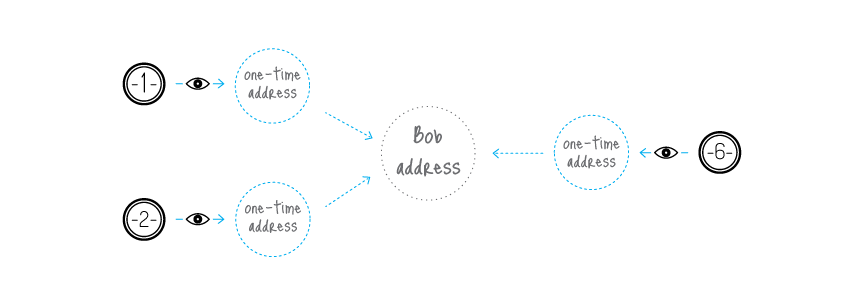 Unlinkable transactions
Unlinkable transactions
An important part of our protocol is usage of random data by the sender. It always results in a different one-time key even if the sender and the receiver both remain the same for all transactions (that is why the key is called 'one-time'). Moreover, even if they are both the same person, all the one-time keys will also be absolutely unique.
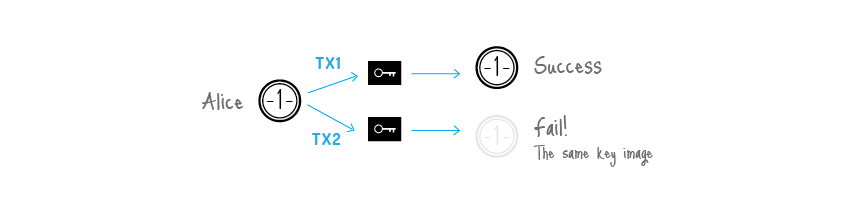
Double-spending proof
Fully anonymous signatures would allow spending the same funds many times which, of course, is incompatible with any payment system's principles. The problem can be fixed as follows.
A ring signature is actually a class of crypto-algorithms with different features. The one UltraNote uses is the modified version of the 'Traceable ring signature' by CryptoNote. In fact it transformed traceability into linkability. This property restricts a signer's anonymity as follows: if he creates more than one ring signature using the same private key (the set of foreign public keys is irrelevant), these signatures will be linked together which indicates a double-spending attempt.
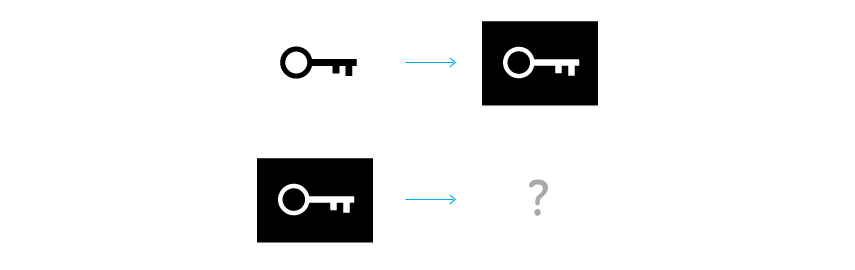
To support linkability UltraNote use a special marker being created by a user while signing, which we called a key image. It is the value of a cryptographic one-way function of the secret key, so in math terms it is actually an image of this key. One-wayness means that given only the key image it is impossible to recover the private key. On the other hand, it is computationally impossible to find a collision (two different private keys, which have the same image). Using any formula, except for the specified one, will result in an unverifiable signature. All things considered, the key image is unavoidable, unambiguous and yet an anonymous marker of the private key.
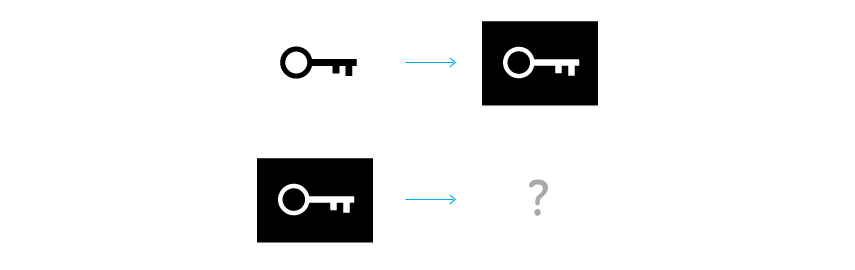 Key image via one-way function
Key image via one-way function
All users keep the list of the used key images (compared with the history of all valid transactions it requires an insignificant amount of storage) and immediately reject any new ring signature with a duplicate key image. It will not identify the misbehaving user, but it does prevent any double-spending attempts, caused by malicious intentions or software errors.
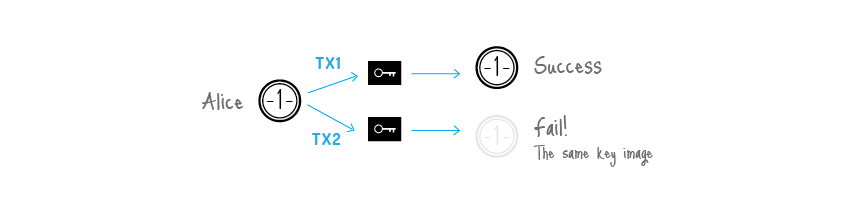 Double-spending check
Double-spending check
UltraNote blockchain analysis resistance
There are many academic papers dedicated to the analysis of the Bitcoin's blockchain. Their authors trace the money flow, identify the owners of coins, determine wallet balances and so on. The ability to make such analysis is due to the fact that all the transfers between addresses are transparent: every input in a transaction refers to a unique output. Moreover, users often re-use their old addresses, receiving and sending coins from them many times, which simplifies the analyst's work. It happens unintentionally: if you have a public address (for example, for donations), you are sure to use this address in many inputs and transactions.
UltraNote is designed to mitigate the risks associated with key re-usage and one-input-to-one-output tracing. Every address for a payment is a unique one-time key, derived from both the sender's and the recipient's data. It can appear twice with a probability of a 256-bit hash collision. As soon as you use a ring signature in your input, it entails the uncertainty: which output has just been spent?
Trying to draw a graph with addresses in the vertices and transactions on the edges, one will get a tree: a graph without any cycles (because no key/address was used twice). Moreover, there are billions of possible graphs, since every ring signature produces ambiguity. Thus, you can't be certain from which possible sender the transaction-edge comes to the address-vertice. Depending on the size of the ring you will guess from 'one out of two' to 'one out of a thousand'. Every next transaction increases the entropy and creates additional obstacles for an analyst.
 Blockchain analysis ambiguity
Blockchain analysis ambiguity
* Source: CryptoNote Foundation!